These are the nine (9) Potential Threats hindering the Promotion of Cloud Computing Industry. The year 2013 is known as the “first year” of the development of the cloud computing industry. Starting from this year, cloud computing will be widely used in terms of technology improvement and application.
According to IDC forecasts, by 2015, the total output value of cloud computing will exceed US$30 billion. At the same time, experts predict that in three years, the average annual compound growth rate of the cloud computing market will reach 91.5%. In 2010, the market size of China’s cloud computing was $11.731 million, and in 2013 it will reach $11.412 million.
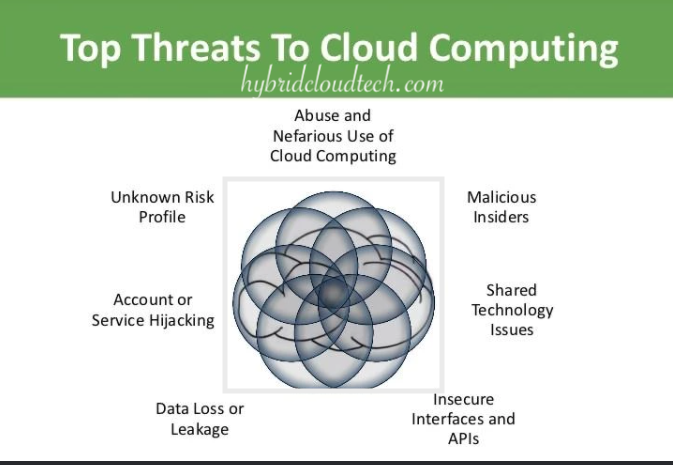
Even though many experts believe that this year is the first year of the industry, users still have doubts about its safety, which directly leads to problems in development. At this stage, the development of the cloud industry still faces nine industry threats:
Threat 1: Data Leakage
The nightmare of data leakage for every CIO is that the sensitive internal data of his company falls into the hands of competitors, which also makes executives sleepless. Cloud computing adds new challenges to this problem. In November 2012, researchers from the University of North Carolina and RSA Corporation released a report showing how on the same physical machine, a virtual machine can use side-channel timing information to extract the private key of another virtual machine. But in many cases, the attacker does not even need such a complicated operation. If a multi-tenant cloud service database is not properly designed, it may cause all customers’ data to suffer due to a vulnerability.
Unfortunately, although data loss and data leakage are serious threats to cloud computing, the measures you take may alleviate one aspect but may make the other more troublesome. Perhaps you can encrypt all data. But if you lose the key, you have lost all your data. Conversely, if you want to back up all your data offline to reduce the impact of catastrophic data loss, but it increases the risk of your data exposure.
Threat 2: Data Loss
Data loss is a very serious problem for both consumers and businesses. The data stored in the cloud may be lost due to other reasons. A cloud service provider’s mistaken operation of deletion, or physical damage caused by natural factors such as fire, may cause the loss of user data, unless the provider does a very good backup job. But the responsibility for data loss is not always only on the supplier’s side. For example, if the user fails to encrypt the data before uploading it, and then loses the key, it may also cause data loss.
Many commitment policies require organizations to conduct continuous audit records or other forms of document archiving for data security. If an organization’s data stored in the cloud is lost, it will cause the organization’s commitment to fall into trouble.
Threat 3: Hijacking Login Details
Account or service traffic hijacking: Hackers hijack innocent users through phishing, fraud, or exploiting software vulnerabilities. Generally, hackers can steal user data from multiple services based on one password, because users will not set up a different password for each service. For the provider, if the stolen password can log in to the cloud, the user’s data will be eavesdropped and tampered with, and the hacker will return false information to the user or redirect the user’s service to a fraudulent website. It will not only cause losses to users themselves, but also affect the reputation of suppliers.
Account and service hijacking and the often accompanying certificate theft are still at the forefront of threats. After the certificate is stolen, the attacker can usually enter some key areas in the cloud service, destroying its confidentiality, integrity, and availability. Enterprise organizations should take necessary precautions against this technical means and adopt some deep-level defense methods to protect data from the risk of leakage. At the same time, the sharing of account credentials between users and services should be prohibited, and a two-factor authentication mechanism should be adopted if necessary.
Threat 4: Service Traffic Hijacking
The nightmare of account or service traffic hijacking for every CIO is that the sensitive internal data of his company falls into the hands of competitors, which also makes executives sleepless. Cloud computing adds new challenges to this problem. In November 2012, researchers from the University of North Carolina and RSA Corporation released a report showing how on the same physical machine, a virtual machine can use side-channel timing information to extract the private key of another virtual machine. . But in many cases, the attacker does not even need such a complicated operation. If a multi-tenant cloud service database is improperly designed, a vulnerability may cause damage to all customers’ data.
Most providers are working hard to strengthen the security mechanisms of their services, and for consumers, they may not have a good understanding of the security issues they may involve in the process of using, managing, and monitoring cloud services. Weak interfaces and API settings will cause organizations to fall into many security issues, affecting confidentiality, availability, and so on.
Threat 5: Service Attacks
To put it simply, a denial of service attack refers to an attack method used by an attacker to prevent normal users from accessing cloud services. It is usually forcing some key cloud services to consume a lot of system resources, such as processing processes, memory, hard disk space, and network bandwidth, causing the cloud server to respond very slowly or not respond at all.
Denial of service attacks (DDoS) have caused a lot of trouble and have been paid attention to by the media. Their attacks may have no substantive purpose. Asymmetric application-level denial of service attacks target the vulnerability of web servers, databases or other cloud computing resources, and then run a small piece of malicious program on the application, sometimes even less than 100 bytes.
When you encounter a denial of service attack during peak traffic, it is like encountering a traffic jam. You cannot access the target server, and you can do nothing except wait for you. For consumers, service interruption will not only dampen their confidence in cloud services, but also cause them to consider moving critical data from the cloud to reduce losses. To make matters worse, because the charging model of cloud services is usually calculated based on how much system resources the user consumes and how much space is occupied, even if an attacker does not completely paralyze your system, it will cause you to use huge resources. Consume and suffer huge cloud service costs.
Threat 6: Internal Malicious Insiders
Malicious insiders: In the security industry, the threats posed by malicious insiders have become a controversial topic. Disputes are controversies, in fact this kind of thing does exist. Malicious insiders that pose a threat to the organization may be incumbent or former employees, contractors, or other business partners who have access to the corporate organization network, system, and database. They abuse their permissions and cause the confidentiality of the corporate organization’s systems and data. Sexuality, integrity, and availability are compromised.
Internal malicious personnel, such as system administrators, have access to sensitive information and key areas of the enterprise. From IaaS to PaaS and SaaS, more and more sensitive areas can be accessed by malicious insiders, even data. Therefore, those systems that rely entirely on cloud service providers for security management are facing huge risks. Even if it is encrypted, if the customer does not have a good grasp of the key or restricts the available time period, the system may face threats from malicious insiders.
Threat 7: Abusing Cloud Services
One of the most powerful advantages of abusing cloud services is that it allows even the smallest enterprises to use the largest amount of computing resources. For most companies, they can’t afford hundreds or thousands of servers, and using hundreds or thousands of cloud servers is no problem. However, not everyone can make good use of this resource.
For example, if an attacker wants to crack a key, it may take several years to use his own machine, while using the powerful computing power of a cloud computing server, it may be done in a few minutes. Or attackers may use cloud servers to conduct DDoS attacks, store malware or pirated software.
Need to consider this threat, more cloud service providers. The number of such incidents has been increasing. How to prevent others from misusing the services you provide? How to define “abuse”? How to prevent this from happening again?
Threat 8: Insufficient Awareness
Insufficient censorship, cost reduction, operational efficiency, and improved security. These advantages make people rush to cloud computing. For those companies that have the resources and the ability to rationally use cloud technology, this is indeed a very real goal, but many companies actually In the tide of swarming, there is no real clear understanding of the full picture of this technology.
If you don’t have a sufficient understanding of the cloud service provider’s environment, applications, and operational responsibilities (such as accident responsibilities, encryption issues, security monitoring), etc., enterprise organizations may face various unknowns with insufficient awareness if they rashly adopt cloud computing Risk, this is probably more serious than the immediate risk.
Organizations that rashly adopt cloud services may fall into multiple problems themselves. Contractual issues such as responsibilities, obligations, transparency between suppliers and customers, and service conformity. After migrating applications that rely on complete network-level security control to the cloud, it will be very troublesome and dangerous if the control is lost or the service provided by the supplier does not meet the needs of the customer. Unknown operational and architectural issues can also cause various problems as application designers and architects lack communication with customers.
The bottom line for enterprises and organizations to migrate to the cloud is that they must have a certain amount of capital capacity, and a sufficiently extensive and detailed review of cloud service providers, and a full understanding of the risks of new technologies.
Threat 9: Shared Technology Vulnerabilities
Sharing technology vulnerabilities Cloud service providers want to deliver large-scale services, they must share infrastructure, platforms, and applications. The design of the components that make up these infrastructures (including CPU cache, GPU, etc.), if there is no good isolation mechanism for multi-tenant architecture (IaaS), redeployment platform (PaaS) or multi-client application (SaaS), then if there is a threat , All service models will face threats. A deep defense strategy must be established, including computing, storage, network, application and user security enforcement and monitoring, regardless of the cloud service model. The key is that there must be a complete vulnerability and misconfiguration resolution mechanism in the entire cloud service.
Searches related to threats to cloud computing
- top threats to cloud computing
- cloud computing threats and vulnerabilities
- what is cloud computing
- new cloud security threats and solutions
- cloud computing risks and benefits
- security issues in cloud computing
- security threats in cloud computing and preventive methods
- risk of cloud computing
The risks of shared technologies such as hypervisors, shared platform components, and shared applications are far more important than customer behavior, because such problems may expose the weaknesses of the entire system to attackers. These vulnerabilities will be very fatal, and the entire cloud system may be paralyzed instantly.