This article contains 14 top Unified Security Management Software. Business functions are increasing every day and with the additional costs of adding resources to manage each one comes the need for a solution that groups and unifies them to a single operating function.
For instance, in human resource management, there are many functions such as complaint and grievance management, remuneration, vacation and o-days permission management, remuneration management, and training. All these functions need to be gathered into one major one to minimize the resources, time and cost used in managing each. This is also the case for information security management.
Unified security management is a single software that provides multiple security functions, making it easier to manage and run than the traditional methods that include running each task separately. It helps an organization by simplifying all security functions and unifying them into one easy-to-understand unit. It is also referred to as Unified Threat Management (UTM) and has quickly gained popularity with many businesses due to its cost-saving element.
List of Top Unified Security Management Software:
Darktrace, Kerio Control, Azure Security Center, Alert Logic Threat Manager, Core Insight Enterprise, REVE Antivirus, Hexadite AIRS, F-Secure, Change Tracker Gen7, Tripwire Enterprise, Qualys, SpyBot, Sophos UTM, Cyberfoam are some of the Top Unified Security Management Software.
What are Unified Security Management Software?
Unified Security Management Software offers full visibility into the threats by identifying emerging threats and ensure regulatory compliance. Unified Security Management Software refers to an application, software or hardware that provides a single security solution for multiple security functions at a single point in the business’s network. The principle behind it is simplicity; the rm does not have to employ services from different vendors for each function. As mentioned earlier, the most admirable quality is the cost- saving.
While traditional approaches involve purchasing dierent security services from dierent vendors, Unified Security Management Software is only bought from one source and contains all security functions. It also minimizes resources such as employees and infrastructure that would be used to administer each function.
Unified Security Management software can be run by a single administrator who takes care of everything from anti-virus to intrusion alerts. Most Unified Security Management programs have user-friendly interfaces that make it easy to interact with, understand, and analyze data then draw viable conclusions.
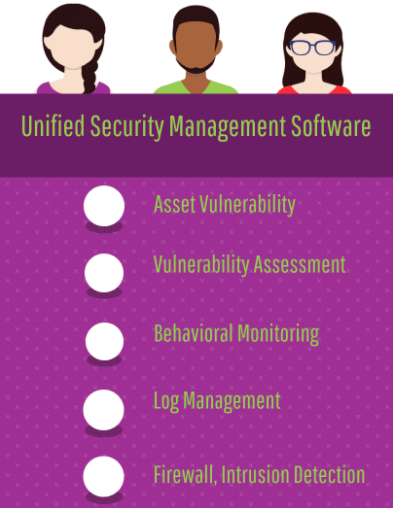
What are Unified Security Management Software
- Asset Vulnerability: Provides features to monitor the vulnerabilities and active threats against different assets including the new assets in your organization.
- Vulnerability Assessment: Assess and report the vulnerabilities.
Behavioral Monitoring: Provides monitoring to spot suspicious network behavior. - Log Management: Provide Log management with other essential tools to give you centralized security monitoring.
- Firewall, Intrusion Detection: The Unified Security Management should be able to protect the network from unauthorized access. It should also function at the application level, allowing only users with authentication to access internal data. Some programs will enable the administrator to assign different privileges to the network users.
Top Unified Security Management Software
Darktrace, Kerio Control, Azure Security Center, Alert Logic Threat Manager, Core Insight Enterprise, REVE Antivirus, Hexadite AIRS, F-Secure, Change Tracker Gen7, Tripwire Enterprise, Qualys, SpyBot, Sophos UTM, Cyberoam are some of the Top Unified Security Management Software.
Top Unified Security Management
- Darktrace
- Kerio Control
- Azure Security Center
- Tripwire Enterprise
- Alert Logic Threat Manager
- Qualys
- Hexadite AIRS
- Change Tracker Gen7
- F-Secure
- REVE Antivirus
- Sophos UTM
- SpyBot
- Cyberoam
1. Darktrace
Protecting corporate networks, cloud and virtualized environments, IoT and industrial control systems, Darktrace autonomously detects and ghts back against emerging cyber- threats across the enterprise. Darktrace’s cyber AI platform uses unsupervised machine learning to analyze network data at scale, and makes billions of probability-based calculations based on the evidence that it sees.
Instead of relying on knowledge of past threats, it independently classfies data and detects compelling patterns. Darktrace is capable of detecting a range of in-progress threats, breaches and vulnerabilities — from IoT hacks and criminal campaigns, through to insider threats or latent vulnerabilities. Darktrace easily integrates with existing infrastructure.
Overview Features
- Real-time threat detection and autonomous response
- Threat Visualizer provides a graphical overview of the day-to-day activity of networks
- Pan-spectrum viewing – higher-order network topology; specic clusters, subnets, and host events
- Searchable logs and events
- Flexible dashboard
- Global threat monitoring in real time using sophisticated self-learning mathematics
Bottom Line
Darktrace is a market leader that provides a strong example of leveraging articial intelligence.
2. Kerio Control
Kerio Control brings together next-generation firewall capabilities – including a network firewall and router, intrusion detection and prevention (IPS), gateway anti-virus, VPN, and web content and application filtering. These comprehensive capabilities and unmatched deployment flexibility make Kerio Control the ideal choice for small and mid-sized businesses.
Preserve the integrity of servers with deep packet inspection and advanced network routing capabilities — including simultaneous IPv4 and IPv6 support. Create inbound and outbound traffic policies, restricting communication by specific URL, application, traffic type, content category and time of day. Kerio Control’s IPS adds a transparent layer of network protection, with Snort-based behavior.
Overview Features
- User authentication via directory services
- MyKerio centralized web based management to monitor and manage multiple Kerio Control deployments
- Bandwidth rules based on time intervals, traffic and content rules, traffic type, users, service, DSCP
- Guest network with captive portal
- Zero-configuration networking
- ICSA Labs certified corporate firewall
Bottom Line
Protect networks from viruses, malware and malicious activity with Kerio Control, the easy-to-administer yet powerful all-in-one security solution.
3. Azure Security Center
Azure Security Center provides unified security management and advanced threat protection across hybrid cloud workloads. Enable adaptive threat protection to reduce exposure to attacks. Block malware and other unwanted code by applying application controls adapted to specific workloads and powered by machine learning. Enable just-in- time, controlled access to management ports on Azure VMs to drastically reduce surface area exposed to brute force and other network attacks. Use advanced analytics and the Microsoft Intelligent Security Graph to get an edge over evolving cyber attacks. Leverage built-in behavioral analytics and machine learning to identify attacks and zero-day exploits. Monitor networks, machines, and the following.
Overview Features
- Advanced threat detection for networks, VMs/servers, and Azure services
- Security event collection and search
- Adaptive application controls
- Centralized policy management – Ensure compliance with company or regulatory security requirements
- Prioritized alerts and incidents – Focus on the most critical threats first with prioritized security alerts and incidents
- Continuous security assessment: Monitor the security posture of machines, networks, storage and data services, and applications to discover potential security issues
Price
Standard – $15 / node / month
Bottom Line
Microsoft Azure Security Center is a set of tools for monitoring and managing the security of virtual machines and other cloud computing resources within the Microsoft Azure public cloud.
4. Alert Logic Threat Manager
Alert Logic Threat Manager for AWS is a network intrusion detection service (IDS) specifically designed for AWS. This service allows users to cost-effectively protect the security of their AWS deployments and meet regulatory compliance mandates, including PCI DSS, SOX, and HIPAA. Threat Manager provides IDS, internal and external vulnerability scanning and PCI scanning abilities via a Security-as-a-Service (SaaS) model that is used today by more than 2,000 customers to monitor security across a variety of network environments. Threat Manager leverages a purposeful grid computing infrastructure as well as Alert Logic’s patented expert system to automatically correlate anomalous behavior patterns to…
Overview Features
- Intuitive dashboard to view compliance status and drill-down a prioritized list of actions needed to maintain compliance
- 24×365 security monitoring, expert incident analysis and live notifications of critical attacks by security analysts
- Management Portal and API: Create new customer accounts, authorize or tear down protected EC2 instances and virtual appliances
- Protocol decoding and validation for network traffic (IP, TCP, UDP, ICMP etc.)
- Anomaly detection and Behaviour based detection
- Vulnerability and exploit signatures
Bottom Line
Alert Logic Threat Manager combines a network intrusion detection system (IDS) with vulnerability management into a single managed security-as-a-service.
Related Posts
- Make Sure Your Security Policies Survive the Transition to the Cloud
- Multi-Factor Authentication (MFA) – Login, Benefits, Examples
- Importance of Web App Security over the Increasing Web Application Attacks
- Working Safely from Home – Online Security Measures in this Pandemic
- IT Security for Companies in the Age of Big Data
5. Core Insight Enterprise
Core Vulnerability Insight (formerly Core Insight) unifies, regulates, and prioritizes vulnerability management initiatives enterprise-wide. Consolidating multiple vulnerability scans across vendors, while matching known exploits and simulating attacks, enables users to focus on the most vulnerable points of their network.
Tailored for complex environments, Core Vulnerability Insight provides a holistic view of your organization’s threat risk. Quickly model potential threat scenarios according to risk criteria most relevant to the business, such as network connectivity, location, vulnerability type, or potential business impact. Adjust which exploits and resulting attack paths are displayed based on the risk they pose to the organization.
Overview Features
- Granular filtering, grouping, and configuration of large amounts of data Centralized Asset Repository
- Interactive Attack Path Mapping: Reach and expose the most valuable business assets
- Smart cards provide an additional layer of security with embedded certificates
- Reports are easily customized (branding, pivot tables, visual charts, etc.) with templates
- Pre-dened connectors to popular vulnerability assessment solutions
Bottom Line
Core Vulnerability Insight consolidates and prioritizes vulnerability management initiatives, while matching known exploits and simulating attacks.
6. REVE Antivirus
REVE Antivirus is a complete cyber security protection solution for PC, Android, iOS, and Windows Phones. It has a higher success rate in detecting and remediating zero-day viruses as it utilizes machine learning algorithms. With REVE Antivirus, team leaders and business owners can rest assured that their employees are using their resources for work.
That is because they can set up app and website authorizations through the software’s administrative panel. And in case an unsanctioned app or website is accessed, managers and owners immediately receive alerts so they can decide on how to act on the matter. Plus, REVE Antivirus…
Overview Features
- Turbo Scan Technology – Fastest scan with high detection rate
- Advanced Rootkit Detection
- Real-time Trojan, Spyware, Botnet & Backdoor protection
- USB Scanner scans external storage devices and provides protection from auto run infections
- Remote management: Remotely manage antivirus license from a single PC via Parental Control
- Advanced real-time protection monitors system behavior in real time
Price
- Antivirus – $10 / month / user
Bottom Line
REVE Antivirus is an IT Security software which provides complete protection from Virus, Spyware, Rootkit & all types of Malware.
7. Hexadite AIRS
Hexadite’s Automated Incident Response Solution (AIRS) is the rst agentless intelligent security orchestration and automation platform for Global 2000 companies. By easily integrating with customers’ existing security technologies and harnessing articial intelligence that automatically investigates every cyber alert and drives remediation actions, Hexadite enables security teams to amplify their ability to mitigate cyber threats in real-time.
Hexadite is changing the way cyber incident response is done, with a fully automated incident response solution that enables organizations to investigate every cyber-alert they receive and close out incidents in minutes, even seconds. Hexadite AIRS can operate without human involvement thanks to its…
Overview Features
- Real-time endpoint protection to identify threats
- Automatic enrichment and querying of host information
- Reputation analysis
- Network protection: Prevent network-based attacks from attacking devices
- Behavior monitoring: Block malicious and suspicious behaviors using advanced runtime analysis
- Exploit protection: Block exploitation of unpatched vulnerabilities including zero-days
Bottom Line
Hexadite solves the cybersecurity capacity problem with the first agentless intelligent security automation and orchestration platform.
8. F-Secure
F-Secure is a European pioneer in cyber security and data protection. They are the only vendor who has consistently received 6 out of 6 for overall protection from the independent AV-Test Organization. F-Secure Business Suite is an on-site solution that continuously offers the best protection for organizations.
It covers the essential parts of security – protection against known vulnerabilities as well as new, emerging threats. Business Suite is a full protection bundle for organizations of all sizes, with advanced control features and support for both physical and virtual environments through one central management tool. Business Suite is designed to cater…
Overview Features
- Best protection levels covering both known vulnerabilities and new, emerging threats
- Excellent administrator control and reporting
- Botnet blocker: Stop external control of compromised assets
- Scanning and reputation server: Offload resource-heavy scanning to a dedicated server
- F-secure proxy: Significantly reduce network traffic
- Policy Manager enables administrators to keep all levels of IT infrastructure safe with automated updates
Bottom Line
F-Secure is a European cyber security company with decades of experience in defending enterprises against everything from opportunistic ransomware infections to advanced cyber-attacks.
9. Change Tracker Gen7
NNT Change Tracker Gen 7 provides continuous protection against known and emerging cyber security threats in an easy to use solution, offering true enterprise coverage through agent-based and agentless monitoring options. Ensure all IT assets are secure and breach free at all times by leveraging state of the art, recommended security and configuration hardening settings along with real-time system vulnerability and configuration drift management.
Change TrackerTM Gen 7 identifies suspicious activity using highly sophisticated contextual change control underpinned by threat intelligence to spot breach activity while reducing change noise. By creating a secure and compliant state for all IT systems…
Overview Features
- Closed Loop Intelligent Change Control ensures that what actually changed, matches the expected approved change prole
- Breach Detection- Host Intrusion Detection
- System Hardening and Vulnerability Management
- Auditor-ready reports help clients spend less time dealing with auditors
- New UI: Mobile app-style web interface
- Scheduled Report operation: Any events, any devices, one-o or repeated
Bottom Line
Ensure critical security controls are in place to spot cyber threats, identify any suspicious changes and adjust the secure baseline for all systems in real time with NNT Change TrackerTM Gen 7.
10. Tripwire Enterprise
Tripwire provides the most comprehensive le integrity solution for the largest enterprises. Additionally, Tripwire detects and judges changes and prioritizes security risks with integrations that provide high value, low volume change alerts. Its robust le integrity monitoring (FIM) solution, monitors detailed system integrity: files, directories, registries, configuration parameters, DLLs, ports, services, protocols and more.
Enterprise integrations provide granular endpoint intelligence that supports threat detection and policy and audit compliance. Tripwire is a host-based IDPS. It runs data integrity checks on the host machine’s state and reports its findings to the user. To perform a difference between the two states, Tripwire first…
Overview Features
- Real-Time FIM and SCM Change Intelligence
- Integrity monitoring and automated remediation workflows
- Automated IT compliance processes: Automates compliance with the industry regulations and standards
- Robust Asset View lets users classify assets with business-relevant tags such as risk, priority, geographic location, regulatory policies
- Performance enhancement offerings: Visible Ops 30/90
- System health checks
Bottom Line
Tripwire Enterprise is a provider of advanced threat, security and compliance solutions to confidently detect, prevent and respond to cyber-security threats.
11. Qualys
Qualys is the leading provider of on demand IT security risk and compliance management solutions – delivered as a service. Secondly, Qualys’ Software-as-aService solutions are deployed in a matter of hours anywhere in the world, providing customers an immediate and continuous view of their security and compliance postures.
A single, dynamic dashboard includes customizable views, graphs and charts giving you a clear and comprehensive view of threat landscape at a glance in real time. Create multiple dashboard views, and break down vulnerabilities by real-time threat indicator (RTI) types, such as zero-day exploits. Craft ad hoc queries with multiple variables and criteria…
Overview Features
- Customized dashboards tailored for different IT and business roles
- Qualys Continuous Monitoring (CM) lets users identify threats and monitor unexpected changes in the network before they turn into breaches
- Powerful data analysis, correlation and reporting engine
- Smart filters for quick lookup based on all the attributes
- Container Sensor is self-updating and can be configured to communicate over proxies
- Automated crawling and testing of custom web applications to identify vulnerabilities including cross-site scripting (XSS)
Bottom Line
Qualys’ suite of fully integrated apps protects digital transformation efforts and meets the needs of all security teams.
12. SpyBot
Spybot is a widely-used, all-inclusive internet protection suite that removes adware, malware, and spyware. Its business editions for corporations and technicians are coupled with anti-virus capabilities and system tools. Spybot immunizes systems by guarding browsers against web-borne threats.
On top of that, the program provides users with tools that allow them to eliminate files that automatically run on startup and taxes a system’s running memory. These preemptive measures ensure that business users continue to perform their tasks without interruptions caused by malignant files. Moreover, Spybot assists businesses in retrieving information destroyed by malware. They can do this with the Boot…
Overview Features
- Task Scheduling feature for configuring automatic updates
- Multi-Core Processors Support
- Command Line Parameters
- Protected Repair Environment
- Rootkit Scanner & Fixer
- Boot CD Creator allows malware detection and cleaning without the interference of malware that the system might be infected with
Price
• Home – $15.99 / month
• Professional – $27.99 / month
Bottom Line
Spybot – Search & Destroy is a powerful tool for cleaning up spyware, adware and other menaces from PCs.
13. Sophos UTM
Sophos UTM is easy to use thanks to the configurable real-time dashboard, flexible modular licensing, and intuitive reusable network object definitions. Easily configure firewall rules that cover multiple destinations, sources, and services, plus country blocking and intrusion prevention (IPS).
Easily control web applications proactively or in real-time using the popular ow-monitor where you can block, shape, or throttle web application traffic on the industry. Protect the network using multi-layered proven protection technologies including Advanced Threat Protection (ATP), IPS, VPN, email and web filtering combined with the industry’s simplest admin interface. Deep Layer-7 inspection (Next-Generation Firewall) ensures true application identification.
Overview Features
- Firewall, VPN, ATP, IPS, email, web filtering and app control
- Built-in Syslog support and automated log backup options
- Built-in reporting on all models
- Two-factor authentication with one-time password (OTP) in many areas
- Integrated wireless controller
- Targeted attack protection, visibility, and analysis
Bottom Line
Sophos UTM provides the ultimate network security package with everything users need in a single modular appliance.
14. Cyberoam
Cyberoam delivers future-ready security to organizations by oering unmatched throughput speeds with its best-in-class hardware along with software to match. Secondly, Cyberoam has been the rst and only vendor in the industry to oer on-appliance reporting with real- time logs and reports, saving the cost of deploying a dedicated reporting solution.
The 1200+ in-depth reports oer real-time visibility into user and network activities, helping organizations to manage security, display compliance and forensic analysis, unmatched by any network security vendor till date. Cyberoam reports include dynamic and animated reports, in-line graphs, and country maps. Cyberoam’s Application Visibility & Control feature enables prioritization of…
Overview Features
- Identity-based Controls with Layer 8 Technology
- Multiple Link Management
- Protection against SQL Injections, Cross-site Scripting (XSS)
- Log Viewer – IPS, Web filter, WAF, Anti-Virus, Anti-Spam, Authentication,System and Admin Events
- Report customization: Custom view and custom logo
- Flexible port configuration
Bottom Line
Cyberoam offers multiple security features that provide robust security to IT systems and proactive remediation of security incidents.
What are Unified Security Management Software?
Unified Security Management Software offers full visibility into the threats by identifying emerging threats and ensure regulatory compliance. Unified Security Management Software refers to an application, software or hardware that provides a single security solution for multiple security functions at a single point in the business’s network. The principle behind it is simplicity; the firm does not have to employ services from different vendors for each function. As mentioned earlier, the most admirable quality is the cost-saving.
What are the Top Unified Security Management Software?
Darktrace, Kerio Control, Azure Security Center, Alert Logic Threat Manager, Core Insight Enterprise, REVE Antivirus, Hexadite AIRS, F-Secure, Change Tracker Gen7, Tripwire Enterprise, Qualys, SpyBot, Sophos UTM, Cyberoam are some of the Top Unified Security Management Software.








